The SEGRID (Security for Smart Electricity GRIDs) project.
To manage all changes that occur in the electricity grid, it will be equipped with intelligent devices for sensing, monitoring, control, automation and communications – the electricity grid evolves to a Smart Grid. The introduction of the Smart Grid in combination with the entrance of many new and inexperienced stakeholders will dramatically increase the threat surface for malicious attacks on the electricity supply. The cyber-attack on the Ukrainian distribution grid in December 2015 is a prominent example of what could happen and a real-life illustration of the resulting impact. Additionally, the Smart Grid will collect and process large amounts of information, which in many instances will be related to the privacy of customers and must be protected against misuse. The SEGRID (Security for Smart Electricity GRIDs) project, sponsored by the European Framework 7 research and development program, addresses the challenges that arise with the introduction of the Smart Grid. Because the SEGRID consortium includes scientific partners, applied research organizations, manufactures and DSO's, the results are scientifically sound but also applicable in practice in the near future.
The Smart Grid will not come into existence overnight; it will be composed of a mix of old, even legacy, and new components. The Smart Grid can be seen as a gradually evolving system in which new functionalities are added to accommodate new use cases with the challenge to maintain security, privacy and dependability of the Smart Grid as a whole. Within the SEGRID project the work has been focused around five concrete use cases:
- Smart meters used for on-line reading of consumption and technical data;
- Load balancing renewable energy centrally;
- Dynamic power management for smart homes, smart offices, and electric vehicles;
- Load balancing renewable energy regionally (substation automation);
- Automatic reconfiguration of the power grid.
These five use cases reflect important steps in the developments of the Smart Grid, and will cover the most relevant security and privacy issues that will arise. The use cases are of increasing complexity and automation (see figure 1).
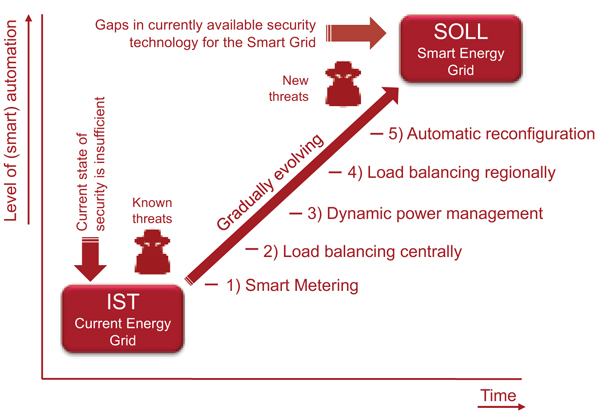
Figure 1: SEGRID use cases
SEGRID will run until the end of 2017 and has already achieved very good results, such as:
- SEGRID Risk Management Methodology – Risk management ensures that effective security controls are implemented in an effi cient and effective way, limiting the exposure to cyber incidents. SEGRID developed the SEGRID Risk Management Methodology (SRMM) that builds on state of the art risk assessment methodologies while providing guidance and enhancements for use in Smart Grids. The SRMM is supported by a tool and by practical guidance for each step of the method. The SRMM applies a stakeholder oriented approach which takes into account the dependency between Smart Grid stakeholders.
- Vulnerability threat modelling – A vulnerability threat modelling tool models a network architecture and all of its components and simulates how diffi cult it is for cyber-attacks to be successful. SEGRID has proposed enhancements to an existing tool called securiCAD, to make it more suitable for use in Smart Grids and for use in operational environments, so that changes in a network architecture can be instantaneously fed into the model and analyzed.
- Security and Privacy Architecture DEsign (SPADE) – The SPADE iterative process has been conceived to design, validate and evaluate security and privacy architectures for Smart Grid systems. The SPADE process produces as fi nal outcome a security and privacy architecture, ready to be deployed to fulfi ll the identifi ed security and privacy requirements, employing Security-by-Design and Privacy-by-Design approaches.
Based on Risk assessments that were conducted, the following security measures were developed and tested:
- Resilient SCADA system – Supervisory Control and Data Acquisition (SCADA) systems form the backbone of critical infrastructures. One of the major threats of SCADA systems is an attacker that gains access to the SCADA system, which can result in a catastrophic scenario. In SEGRID, we have developed a SCADA system that is able to operate correctly even under intrusions. The key idea is to replicate the SCADA system, allowing replicas to deterministically execute the same sequence of requests (e.g., operator commands) in such a way that, despite the failure of a fraction of the replicas, the remaining ones have the same state and ensure correctness of the offered services.
- Resilient communication infrastructure – Smart Grid applications are typically run in equipment inside the (primary) substation and are connected to e.g. the head end system. In SEGRID, we have focused on improving the resilience of the communications outside of the substation, as these are spread over large geographical areas, and consequently are more prone to failures. We have designed and implemented a new Software Defi ned Network (SDN) based solution to manage the network, which connects the primary substations to the control center(s) of a DSO.
- Improved resource management for (D)TLS – In Smart Grid systems, the TLS and DTLS protocols emerge as the de-facto solutions for secure communication between for instance, SCADA units and RTUs in secondary substations. However, the protocol suffers from a severe security vulnerability, which makes (D)TLS servers highly exposed to a Denial of Service (DoS) attack. SEGRID has proposed a solution that neutralizes the DoS attack described above. The proposed solution does not break current standards, and has been successfully tested on real RTUs communicating over a secure DTLS channel.
This work was funded by The EC as part of the EU FP7 SEGRID project under Framework 7 agreement 607109. The views expressed are purely those of the authors and may not in any circumstances be regarded as stating an official position of the EC.
Contact details:
The SEGRID project: www.segrid.eu
Reinder Wolthuis, project coordinator, Senior project manager and consultant cybersecurity
Email: reinder.wolthuis@tno.nl
Tel.: +31 651 913 3792